Understanding the Evolution of Fraud: From Detection to Industrialization
- Mar 29
- 5 min read
Updated: May 3
The Changing Landscape of Fraud Detection
For many of us who worked deeply in fraud control a decade ago, fraud detection was never merely about catching forged paper. It was about learning to read disturbances — the small things that did not fit. A date that did not align. A signature that lacked flow. A field story that sounded rehearsed. A purpose that did not match usage. A document that was technically complete but intuitively wrong.
My own old RCU training material from 2012 was built around exactly that discipline: triggers, patterns, deviations, tell-tale signs, mismatches, factual inconsistencies, custody, investigation process, and root-cause analysis.
That body of work was not theoretical. It came from a period when fraud control in the field demanded observational sharpness. The RCU journals we used and built spoke of fake documents, SHPI evaluation, property titling, signature study, fingerprint identification, bank statement interpretation, customized triggers, fraud reporting, and even the practical problem of proving intent.
Seen together, they reflected a very important truth: fraud was rarely discovered through one grand revelation. It was usually detected through accumulation — small deviations that, when connected, formed a pattern.
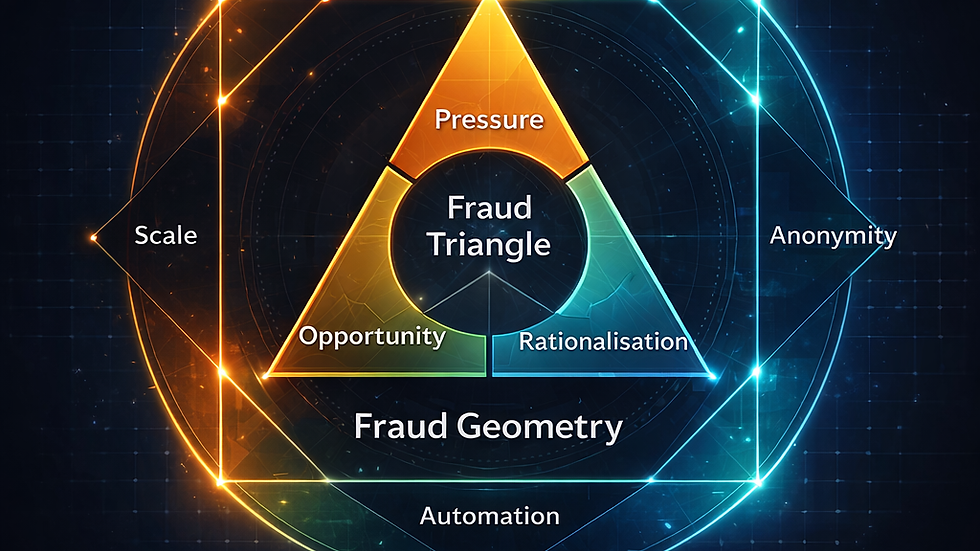
At the center of that older framework sat the classic fraud triangle: pressure, opportunity, and rationalization. My 2012 material explicitly used that model as a foundational lens, and the journals reinforced it repeatedly through discussions on intent, ethics, controls, process, observations, and behavior.
It was, and remains, one of the most useful ways to understand why fraud happens.
Pressure explains the need. Opportunity explains the opening. Rationalization explains the inner permission.
That triangle humanized fraud. It reminded us that fraud is not an abstract event. It is a decision made possible by circumstance, access, and self-justification.
The New Era of Fraud: AI and Deception
And yet, I increasingly feel that in the age of AI-enabled deception, the triangle is no longer enough by itself. Not because it is wrong, but because it no longer fully explains how fraud now scales. That distinction matters.
In the world many of us dealt with earlier, fraud required effort. A forged signature had to be practiced. A fabricated document had to be sourced, altered, or physically created. A misleading field narrative required local coaching. A false bank statement had to survive scrutiny of format, chronology, continuity, and customer profile. Even collusion had a human texture to it.
Our journals from that period reflect this repeatedly — they deal with land records, passbooks, stamps, property titles, identity proofs, signatures, fingerprints, house classifications, account forms, and document-based triggers because fraud still had to travel through human processes and physical evidence.
The Economics of Fraud are Changing
Today, the economics of fraud are changing.
A fraudster no longer needs only motive and opportunity. He may now have machine-assisted capability. He may not need physical proximity. He may not need deep local familiarity. He may not need to fabricate one document at a time. He may not even need a stable identity in the traditional sense.
That is why I believe the fraud triangle needs expansion. Or perhaps more accurately, it needs a new outer structure.
The triangle still explains the motive core of fraud. But around that core, we now need to recognize a new set of fraud multipliers: capability, scale, anonymity, synthetic identity, and automation.
These are not replacements for pressure, opportunity, and rationalization. They are amplifiers.
Capability: The Game Changer
Capability changes the game because fraud is no longer limited by individual skill. Earlier, the fraudster needed to know how to forge, imitate, manipulate, or coordinate. Today, technology can lend capability to people who may not otherwise have possessed it. What once required expertise may now require only access to tools.
Scale: A New Dimension
Scale changes the game because fraud can now be repeated, cloned, and distributed with far lower marginal effort. In the older model, many fraud attempts were constrained by time, geography, and human energy. Much of our RCU work, therefore, focused on spotting patterns across MIS, repeat document issues, deviations, high DD-PD categories, and sampling outcomes. That itself was an early recognition that scale changes risk. AI simply pushes that principle much further.
Anonymity: The Hidden Threat
Anonymity changes the game because the distance between act and actor increases. Traditional fraud often left behind stronger traces of physical handling, local linkage, or visible collusion. Today, deception may be staged through digital layers that weaken attribution and delay response.
Synthetic Identity: The New Reality
Synthetic identity changes the game because the fraud event may no longer depend on impersonating one real person. It may involve constructing a convincing but partly artificial reality. In the old world, we were trained to spot mismatches between applicant, document, field visit, purpose, and profile. In the new world, the challenge may be deeper: what if the profile itself is synthetically coherent?
Automation: The Systematic Approach
Automation changes the game because fraud is no longer only an act. It can become a system. When deception acquires workflow, repeatability, and adaptive feedback, it stops being episodic and begins to resemble production.
This, to me, is the real shift.
Fraud is moving from being a personal act of deception to an industrialized architecture of deception. And once that happens, our frameworks must evolve accordingly.
Revisiting Old Lessons in a New Context
This is where the lessons of the older RCU discipline become surprisingly relevant again. The answer is not to discard old fraud thinking. In fact, those older journals hold enduring value precisely because they were grounded in observation, domain knowledge, chronology, mismatch analysis, and root-cause logic.
One of the strongest themes in that material was that the process of fraud detection begins with seeing what does not fit — triggers, patterns, deviations, factual inconsistencies, purpose mismatches, documentation anomalies, and behavioral signals. That instinct remains invaluable.
But instinct alone will not be enough.
If fraud has acquired digital capability, institutional defense cannot remain frozen at checklist vigilance. Many institutions, especially banks, still operate largely through rules, thresholds, static controls, limited predictive models, and fragmented review processes. Their fraud frameworks are often still built to catch yesterday’s deviations. Meanwhile, deception is becoming more contextual, more personalized, and more scalable. That creates asymmetry.
The Asymmetry of Fraud Detection
Tomorrow’s fraud is beginning to meet yesterday’s controls.
This is not merely a technology issue. It is also a governance issue. Boards, investigators, auditors, credit teams, operations teams, legal teams, and policymakers may all need to revisit the language with which fraud is understood. If we continue to rely only on motive-based models without incorporating capability-based multipliers, we may end up underestimating risk not because we missed the pressure, opportunity, or rationalization — but because we failed to appreciate the speed, scale, and realism with which deception can now be manufactured.
So perhaps the way forward is not to abandon the fraud triangle, but to place it inside a broader frame.
The triangle still tells us why fraud begins. But fraud geometry must now also tell us how fraud expands.
The Broader Geometry of Fraud
That broader geometry, in my view, includes: Pressure. Opportunity. Rationalization. Capability. Scale. Anonymity. Synthetic Identity. Automation.
The older triangle explained the psychology of fraud. The emerging geometry must explain its industrialization.
That is the shift we need to think about. Because fraud is no longer only about spotting forged paper. It is increasingly about detecting fabricated reality.
Disclaimer: This note draws on publicly reported developments and personal reflections from prior fraud-control experience. The views expressed are personal and intended to provoke thought on evolving fraud risks, not to comment on any specific institution, platform, or incident beyond what is already in the public domain.









Comments